Designing a Proxy Server Implementation
Before you can design a Proxy Server implementation and install Proxy Server, you need to be knowledgeable on a number of concepts:
-
IP routing concepts
-
Firewalls concepts
-
Packet filtering concepts
-
Files and protocols utilized in Web applications
To design a Proxy Server implementation, there are a number of factors that has an impact on the Proxy Server design:
-
The characteristics of data that will pass to the Proxy Server. Data characteristics should include factors such as the quantity of data which you expect the Proxy Server to handle, and whether data confidentiality needs to be ensured.
-
The type of firewall that the Proxy Server will interface with.
-
Decide whether the Proxy Server will be located within the DMZ or on the edge of the network.
-
Determine the correct sizing of Proxy Server(s).
-
The resources located on the private network which Internet users should be able to access.
-
The physical layout of the servers
-
The connections to and from proxy servers.
-
The volume of expected network traffic.
-
Bandwidth between sites.
-
Who needs access to the Proxy Server, and what type of access is required.
-
Determine the time which users should be able to access the Proxy Server.
-
Future network expansion.
-
Existing proxy server configuration: Here, factors such as the location of an existing proxy server, the WAN connections being used, and the protocols used in the private network should be considered.
After you have looked at all the factors which impact the Proxy Server design, you have to determine, or select between a few additional design elements:
-
The type of connection that the Proxy Server must support:
-
Persistent connections
-
Nonpersistent connections
-
-
The type of services that the Proxy Server must provide:
-
Web Proxy
-
WinSock Proxy
-
Socks Proxy
-
Packet filtering
-
Reverse Web Proxy
-
-
The types of connection technology that the Proxy Server must support:
-
Digital Subscriber Line (DSL)
-
Integrated Services Digital Network (ISDN)
-
Public Switched Telephone Network (PSTN)
-
T1
-
X.25
-
-
The type of Proxy Server clients that the Proxy Server must support.
-
The type of routing which each router should support:
-
Dynamic routing
-
Static routing
-
-
Whether multiple proxy servers will be implemented to improve performance and provide high levels of availability. Proxy Server provides a feature called proxy arrays. A proxy array is a solution whereby one or multiple proxy servers operate as a single cache for client requests. Benefits provided by the proxy array feature include scalable performance, and fault tolerance.
You can create a Proxy Server design where frequently requested content is cached. Proxy Server can locally cache Internet sites and files which are frequently requested. Subsequent requests for these Internet sites are then serviced from the local cache. Cached information is accessed by users from a location on the Local Area Network (LAN). This design has a number of benefits. For instance, bandwidth utilization to the Internet ends up being reduced because cached information does not need to be downloaded from the Internet. All of this leads to an improvement in the service experienced by users.
With passive caching, Proxy Server stores objects in the Proxy Server cache with each object obtaining a Time To Live (TTL) value. Before Proxy Server forwards requests to the Internet, it first checks the Proxy Server cache to determine if the request can be serviced from there. Active caching works together with passive caching. With active caching, Prox Server automatically generates requests for specific objects in the Proxy Server cache so that frequently requested objects remain cached.
The requirements for creating a Proxy Server design that caches content are listed here:
-
Web content is only cached on NTFS partitions. This basically means that you need to have, minimally, one NTFS partition that is capable of storing frequently accessed Web content.
-
You should have two network adapters so that private network traffic with Internet traffic can be separated. This results in network congestion being reduced.
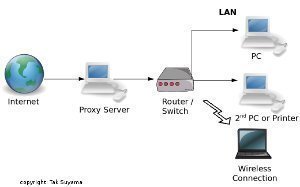
You should place proxy servers using their purpose or function as the basis to determine placement. This concept is illustrated here:
-
If the Proxy Server is to provide connectivity between the private network and the Internet;
-
Place the Proxy Server between the private network and the Internet.
-
-
If the Proxy Server is to cache Web content so that frequently accessed content can be accessed from the local cache;
-
Place the Proxy Server local to those users requesting the content.
-
-
If the Proxy Server is to is to provide both connectivity between the private network and the Internet and cache Web content;
-
Place the Proxy Server between the private network and the Internet, and local to those users requesting the content.
-
The following information has to be defined for every interface in the Proxy Server implementation:
-
The type of connection (persistent/nonpersistent) between the router interface and the network.
-
The following IP information for interfaces that are connected to IP network segments:
-
IP address configuration.
-
IP subnet mask configuration.
-
-
The following IPX information for interfaces that are connected to IPX network segments:
-
IPX network number.
-
IPX frame type
-
Another component that should be included when you plan your Proxy Server implementation is to determine the client operating systems that Proxy Server should support. Proxy Server can support a number of different client operating systems.
You should define Proxy Server client support based on what your Proxy Server implementation should provide:
-
Define Windows Proxy Server client support for the following reasons:
-
All Windows operating systems should be supported.
-
IP traffic needs to be redirected through Proxy Server Support IPX to IP gateways.
-
Clients should utilize the local address table (LAT) to determine the destination IP addresses.
-
-
Define default gateway support for the following reasons:
-
All operating systems should be supported – the default gateway will be configured to pass all nonlocal to Proxy Server.
-
-
Define Microsoft Internet Explorer 5.0 support for the following reasons:
-
All operating systems that include Internet Explorer 5.0 should be supported.
-
Only HTTP and FTP traffic will pass through Proxy Server.
-
The Internet Explorer Administrator Kit (IEAK) is to be used to administer Proxy Server client configuration.
-
-
Define SOCKS support for the following reasons:
-
Support for Unix and Macintosh is ensured.
-
All operating systems that utilize SOCKS standard should be supported
-
IPs supported by SOCKS applications should be redirected.
-
Another planning component that should be included when you design your Proxy Server implementation is to determine the level of data protection that should be configured.
-
Inbound and outbound packet filters can be configured to filter and restrict traffic, based on the criteria defined for the different IP traffic types.
-
Domin filters can be configured to restrict Internet access to only certain IP addresses or FQDNs. In a domain filter, you can include a number of Internet sites and then define the action that the domain filter should take when a request is received for one of these sites: Reject packets for these specific Internet sites and forward all other packets OR forward packets to these specific Internet sites and reject all other packets. Domain filters can restrict outbound traffic, based on a single computer or the IP address of a cluster, an IP address range or a FQDN.
-
You can utilize Proxy Server user authentication to specify Internet access, based on user or group account.
-
Through Web publishing, you can restrict inbound traffic based on the URL requests of Internet users.
The default configuration of Proxy Server is to drop the URL requests of Internet users. This means that Internet users do not have access to Web and FTP servers hosted within the private network, by default. You can though define URLs where requests for these URLs should be passed to Web and FTP servers on the private network. Proxy Server will allow URL requests when you define them in the Web Publishing list.
For URLs that are requested which are defined in the Web Publishing list, Proxy Server passes the requests to the Web and FTP servers on the private network.
For URLs that are requested which are not defined in the Web Publishing list, Proxy Server performs either of the following:
-
Drops the request.
-
Forwards the request to a default Web site hosted on the computer hosting Proxy Server.
There are also a number of techniques that optimize Proxy Server performance, which you should consider implementing:
-
Caching Web content improves performance. Cached information is accessed by users from a location on the Local Area Network (LAN). This means that bandwidth utilization to the Internet ends up being lowered because cached information does not need to be downloaded from the Internet. All of this leads to an improvement in the service experienced by users.
-
Proxy Server also provides a feature called proxy arrays. A proxy array is a solution whereby one or multiple proxy servers operate as a single cache for client requests. Benefits provided by the proxy array feature include scalable performance, and fault tolerance.
-
Network Load Balancing (NLB) can be used to distribute the processing load of inbound traffic over multiple proxy servers. This leads to high availability and performance optimization.
-
Round Robin DNS can also be used to load balance inbound traffic across multiple proxy servers, thereby also providing high availability and performance optimization.
The advantages of using proxy arrays as a Proxy Server optimization method when you implement Proxy Server are listed here:
-
Because Web content is cached over multiple servers, no single server hosts all Web content.
-
If a server in the proxy array fails, failover is immediately provided.
The advantages of using Network Load Balancing (NLB) as a Proxy Server optimization method when you implement Proxy Server are listed here:
-
You can add or remove proxy servers residing in the NLB cluster.
-
Load balancing occurs dynamically over all proxy servers residing in the NLB cluster.
-
Because load balancing and the addition or removal of proxy servers occurs dynamically, availability and performance is improved.
-
The NLB cluster is automatically reconfigured when a proxy server happens to fail.
The advantages of using Round Robin DNS as a Proxy Server optimization method when you implement Proxy Server are listed here:
-
Load balancing is performed on all proxy servers in the round robin DNS.
-
Round Robin DNS can operate on all operating system platforms.
-
Performance is improved because traffic is basically load balanced over all proxy servers.
If you need to provide the highest possible level of server availability for your Proxy Server implementation, you should use Microsoft Windows Clustering. Using Microsoft Windows Clustering provides the following benefits for your Proxy Server implementation:
-
The Proxy Servers all share a common cache.
-
If a server in the proxy array fails, failover is immediately provided.
-
Because the cache does not need to be built again when a server fails, restore occurs quite faster.
To optimize Internet access, you can include the following Proxy Server caching methods in your Proxy Server design:
-
As mentioned previously, with passive caching, Proxy Server stores objects in the Proxy Server cache with each object obtaining a Time To Live (TTL) value. Before Proxy Server forwards requests to the Internet, it first checks the Proxy Server cache to determine if the request can be serviced from there. When the Proxy Server cache becomes full, Proxy Server removes objects from the cache, based on a combination of factors: object size, object age, and object popularity
The advantages of using passive caching in your Proxy Server implementation are:-
The Internet connection is only initiated when users need to access the Internet.
-
No activity occurs when users are not accessing the Internet.
-
-
With Active Caching, Proxy Server automatically generates requests for specific objects in the Proxy Server cache so that frequently requested objects remain cached. Proxy Server determines which objects should be flagged for active caching by considering object popularity, Time To Live (TTL) value of objects, and server load to determine the level of active caching performed.
The advantages of using active caching in your Proxy Server implementation are:-
Processor overhead is reduced.
-
Internet traffic is reduced during times of peak utilization.
-
Determining Proxy Server Hardware and Software Requirements
Proxy Server has a few minimum hardware and software implementation requirements. However, depending on the size of the organization, existing hardware and software, future network expansion, and expected traffic volumes; the Proxy Server implementation requirements between organizations would differ. For each different network environment, there are different requirements for a Proxy Server implementation.
The requirements listed below merely serves as a guideline on the hardware requirements for a Proxy Server implementation:
-
Processor; Intel 486 or faster supported RISC-based microprocessor
-
Disk space; 10 MB available disk space for Proxy Server
-
For caching; 100 MB plus an additional 0.5 MB for each Web Proxy service client.
-
RAM; at least 24 MB. For RISC-based systems, this increases to 32 MB.
-
An NTFS formatted partition to store the Proxy Server cache.
-
A network adapter card for connection to the LAN.
-
A network interface configured for the Internet.
When planning a Proxy Server implementation, you have to decide on the hardware that you will used to establish connections to the Internet:
-
ISDN lines can be used to establish connections to the Internet. ISDN is a digital dial-up service that utilizes telephone cabling and other technology to provide Internet connections. The different types of ISDN services are ISDN Basic Rate Interface (BRI) and ISDN Primary Rate Interface (PRI).
The main characteristics of ISDN Basic Rate Interface (BRI) are listed here:-
BRI connections work well for small companies
-
BRI connections are available from quite a number of telephone companies.
-
ISDN BRI can offer 128 Kbps of bandwidth.
-
Provide e-mail for a maxmum of 20 concurrent users.
-
Provide large FTP downloads for only 3 to 4 simultaneous users.
-
Provide Web browsing for 6 to 8 concurrent users.
The main characteristics of ISDN Primary Rate Interface (PRI) are listed here:
-
ISDN PRI can offer 1.544 Mbps transmission speed.
-
Provide e-mail for a maximum of 120 concurrent users.
-
Provide large FTP downloads for only 40 to 50 simultaneous users.
-
-
Dial-up modem connections are ideal if your organization only consists of a small number of users that do not need to connect to the Internet on a regular basis. This is due to dialup modem connection only being able to meet the bandwidth requirements of a small number of users. Modems can be installed on a computer, and then shared through the Windows Internet Connection Sharing (ICS) service.
A few characteristics of dial-up modem connections are:-
A dial-up modem connection can only reach up to 53 Kbps.
-
Provide e-mail for a maximum of 10 concurrent users.
-
Provide large FTP downloads for only 1 to 2 simultaneous users.
-
Provide Web browsing for 2 to 3 concurrent users.
-
You also have to decide on the hardware which will be utilized to connect the server to the Internet:
-
Analog modem: Analog modem run at 28.8 or 33.6 Kbps speeds. An analog modem is ideal for a single user connecting to the Internet, and for a networked server gateway.
-
ISDN adapters: This is the popular choice. The ISDN adapters dial an ISDN access number and then maintain the particular connection.
-
Routers: Routers are networking devices that connect networks.
Installing Proxy Server
You should verify a number of things before you actually install Proxy Server:
-
10 MB available disk space for Proxy Server and 100 MB plus an additional 0.5 MB for each Web Proxy service client.
-
An NTFS formatted partition to store the Proxy Server cache.
-
TCP/IP should be installed on the computer.
-
The internal network interface should be bound to the TCP/IP or IPX/SPX protocol being used on the LAN.
-
You should configure the software for two network adapter cards before you attempt to install Proxy Server.
When Proxy Server is installed, the following changes are made to the computer on which you are installing it:
-
The Web Proxy service is installed.
-
The WinSock Proxy service is installed.
-
The Socks Proxy service is installed.
-
Each of these services is added to the Internet Service Manager administration tool.
-
The local address table is installed.
-
On the NTFS volume, the cache drive is created.
-
The client installation and configuration software is copied.
-
The Mspclnt shared folder is created.
-
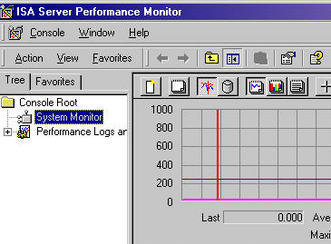
The Proxy Server Performance Monitor counters are installed.
-
The HTML online documentation is installed.
How to install Proxy Server
-
On the Proxy Server installation CD, proceed to run Setup.
-
Click Continue on the Welcome to the Microsoft Proxy Server Installation program screen.
-
The Microsoft Proxy Server Setup page opens.
-
Specify the 10-digit product key provided on the CD-ROM case. Click OK.
-
The Microsoft Proxy Server Setup dialog box displays the default destination folder and the Installation Options button. Click the Installation Options button.
-
The Microsoft Proxy Server – Installation Options dialog box opens, displaying all components as being selected. Click Continue.
-
Setup now stops the Web services.
-
The Microsoft Proxy Server Cache Drives dialog box opens. Caching is by default enabled.
-
The local drives of the server are listed in the Drive box.
-
Select the drive which should be used to store cached data. In the Maximum Size (MB) box, enter th appropriate value. Click Set, and then click OK.
-
The Local Address Table Configuration dialog box opens.
-
Click the Construct Table button.
-
The Construct Local Address Table dialog box opens.
-
Select Load from NT internal Routing Table to select the network adapter cards thats IP addresses must be added to the local address table.
-
Select the Load known address ranges from the following IP interface cards option, and then select the network adapter. Click OK.
-
Click OK to acknowledge the message displayed, indicating that the IP addresses have been loaded into the local address table.
-
The Local Address Table Configuration dialog box opens, displaying IP addresses in the Internal IP Ranges box.
-
Check that the addresses defined are correct, and then click OK.
-
The Client Installation/Configuration dialog box opens.
-
Enter the appropriate information and verify that the correct computer name is displayed in the Computer name field and Proxy field.
-
If you enable the Automatically configure Web browser during client setup checkbox, the Web browser network configuration setting of the client is changed so that client requests are sent to the Proxy Server, and not to the Internet.
-
Click Configure.
-
You can either run the default script to configure the client Web browser, or alternatively, you can use a custom URL.
-
Click Properties located beneath Browser automatic configuration script.
-
The Advanced Client Configuration dialog box opens.
-
Specify whether the Proxy Server is utilized for local servers.
-
Specify the IP addresses that should be excluded from Proxy Server.
-
Specify the domains that should be excluded from Proxy Server.
-
Specify a backup to the proxy server.
-
Click OK.
-
The Access Control dialog box opens.
-
Verify that access control is specified for the Web Proxy service and for the WinSock Proxy service and then click OK.
-
The Proxy Server Setup files are copied to the computer.
-
When the Setup Information dialog box opens, click OK. The Setup Information dialog box displays information on the packet filtering feature. The packet filtering feature is not automatically enabled when Proxy Server is installed. Click OK.
-
A Proxy Server 2.0 Setup was completed successfully message is displayed.
How to install WinSock Proxy Client on client computers
When you install WinSock Proxy Client on client computers, the following changes are made:
-
The Proxy Client program group is created
-
The local address table file, Msplat.txt, is installed on the client. Proxy Server will update this file.
-
Mspclnt.ini is also copied to the client.
-
The WSP Client icon is added to Control Panel. This only occurs for Windows 3.x, Windows 95, and Windows NT clients.
-
Remote WinSock from WinSock Proxy Client replaces Winsock.dll. This would enable the computer to only access Internet sites using the WinSock Proxy service.
To install WinSock Proxy Client on a client computer;
-
Open Internet Explorer
-
In the Address box, enter http://proxycomputername/msproxy.
-
The WinSock Proxy Client 2.0 Installation page is displayed.
-
To install WinSock Proxy Client, click WinSock Proxy 2.0 client.
-
Click the Open it option and click OK.
-
The Microsoft Proxy Client Setup dialog box opens.
-
Click Continue to proceed with the installation.
-
Click Install Microsoft Proxy Client to start copying Setup files to the client computer.
-
Click OK.
-
The Setup – Restart System dialog box opens.
-
Click the Restart Windows Now option.
How to add or remove Proxy Server components
-
On the Proxy Server installation CD, proceed to run Setup.
-
Click Add/Remove on the Setup screen.
-
Follow the instruction displayed to add or remove Proxy Server components.
How to restore Proxy Server settings or files
-
On the Proxy Server installation CD, proceed to run Setup.
-
Click Reinstall on the Setup screen.
-
Follow the instructions displayed to restore Proxy Server settings/files.
How to remove Proxy Server from the server
-
On the Proxy Server installation CD, proceed to run Setup.
-
Click Remove All on the Setup screen.
-
Click Yes to acknowledge that you want to remove Proxy Server.
-
Proxy Server is then removed from the server.
How to disable WinSock Proxy Client
-
Open Control Panel.
-
Double-click WSP Client.
-
Deselect the Enable WinSock Proxy Client checkbox.
-
Restart the computer.
How to re-enable the WinSock Proxy Client
-
Open control Panel.
-
Double-click WSP Client.
-
Check the Enable WinSock Proxy Client checkbox.
-
Restart the computer.
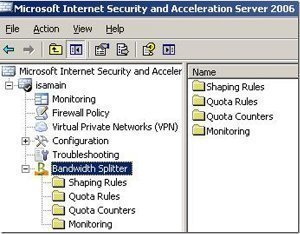
Administering Proxy Server using the Internet Service Manager
You can use the Internet Service Manager to configure properties for the Web Proxy, WinSock Proxy, and Socks Proxy services of Proxy Server.
To open the Internet Service Manager;
-
Click Start, click Programs, click Microsoft Proxy Server, and then click Internet Service Manager.
-
You can open the properties of specific Proxy Server service by double-clicking the computer name displayed alongside the particular service name.
There are some properties settings which are common for all three Proxy Server services, and there are others that are relevant for only a particular Proxy Server service. This concept is illustrated here.
-
The properties settings which can be configured for the Web Proxy service are listed here:
-
Service
-
Permissions
-
Caching
-
Routing
-
Publishing
-
Logging
-
-
The properties settings which can be configured for the WinSock Proxy service are listed here:
-
Service
-
Permissions
-
Protocol
-
Logging
-
-
The properties settings which can be configured for the Socks Proxy service are listed here:
-
Service
-
Permissions
-
Logging
-
The configuration settings which you can view and configure on the Service tab for each of the three Proxy Server services are listed below:
-
View the product release.
-
Verify the product ID.
-
Add additional information on the service.
-
Add additional information on the server.
-
View the current sessions.
-
Navigate to the Shared services tabs.
-
Navigate to the Configuration tabs.
The configuration settings which you can view and configure on the Permissions tab for the Web Proxy and WinSock Proxy services are listed below:
-
Select or disable the Enable access control checkbox.
-
Select the Protocol when defining user or group permissions. Permissions are basically assigned for each protocol.
-
Define user and group permissions for using the Internet protocols.
The configuration settings which you can view and configure on the Permissions tab for the Socks Proxy are:
-
Specify the source and destination for an entry, and then define whether requests should be allowed or defined.
The configuration settings which you can view and configure on the Caching tab for the Web Proxy and service is listed here:
-
Select the Enable caching checkbox and then select between the following Cache expiration policy options:
-
Updates are more important.
-
Equal importance.
-
Fewer network accesses are more important
-
-
Select the Enable active caching checkbox and then select between the following options:
Faster user response is more important.
-
Equal importance.
-
Fewer network accesses are more important.
-
The configuration settings which you can view and configure on the Routing tab for the Web Proxy and service is listed here:
-
For upstream routing, you can select between the following options:
-
Use direct connection.
-
Use Web proxy or array.
-
-
If you select the Enable backup route checkbox, you can select between the following options:
-
Use direct connection.
-
Use Web proxy or array.
-
-
You can also select the Resolve Web proxy requests within array before routing upstream checkbox on this tab.
The configuration settings which you can view and configure on the Publishing tab for the Web Proxy and service is listed here:
-
Enable/disable Web publishing.
-
Configure computers to publish information on the Internet via the Proxy Server.
-
Specify what should happen to incoming Web server requests:
-
Discard
-
Sent to the local Web server.
-
Sent to another Web server.
-
The configuration settings which you can view and configure on the Logging tab for all three Proxy Server services are listed below:
-
Enable/disable logging. When enabled, the following types of information will be logged:
-
Server
-
Client
-
Connection
-
Object
-
-
Specify the Log to file option, or the Log to SQL/ODBC database option.
-
Specify when a new log should be opened.
-
Specify the log file directory.
-
How to disable IP routing (control access to the private network)
-
Open Control Panel
-
Double-click Network.
-
The Network dialog box opens.
-
Click the Protocols tab.
-
Select TCP/IP, and click Properties.
-
The TCP/IP Properties dialog box opens.
-
Switch to the Routing tab.
-
Ensure that the Enable IP Forwarding checkbox is not selected (blank).
-
Click OK.
How to configure publishing configuration settings for the Web Proxy service
-
Open Internet Service Manager.
-
Double-click the computer name alongside the Web Proxy service.
-
The Web Proxy Service Properties dialog box opens.
-
Click the Publishing tab.
-
Select the Enable Web publishing checkbox.
-
If you want to drop all incoming Web server requests, click the Discard option.
-
If you want to forward all incoming Web server requests to IIS on the Proxy Server computer, click the Sent to the local Web server option.
-
If you want forward all incoming Web server requests to a specific downstream server, click the Sent to another Web server option.
-
If you want to configure the default Web server host, click Default Mapping.
-
The Default Local Host Name dialog box opens.
-
Provide the name of the default server. Click OK.
-
Click Apply and click OK.
How to enable dynamic packet filtering
-
Open Internet Service Manager.
-
Double-click the computer name alongside the Web Proxy service.
-
The Web Proxy Service Properties dialog box opens.
-
Click the Security button on the Service tab.
-
Click the Packet Filters tab.
-
On the Packet Filters tab, click the Enable packet filtering on external interface checkbox.
-
Select the Enable dynamic packet filtering of Microsoft Proxy Server packets checkbox.
-
Click OK.
-
Click OK in the Web Proxy Service Properties dialog box.
How to create a packet filter using predefined protocol definitions
-
Open Internet Service Manager.
-
Double-click the computer name alongside the Web Proxy service.
-
The Web Proxy Service Properties dialog box opens.
-
Click the Securty button on the Service tab.
-
Click the Packet Filters tab.
-
On the Packet Filters tab, click Add.
-
When the Packet Filter Properties dialog box opens, click the Predefined filter option.
-
Select a protocol from the available Protocol ID list.
-
In the Local host area of the Packet Filter Properties dialog box, select the appropriate option to allow packet exchange with a host.
-
In the Remote host area of the Packet Filter Properties dialog box, specify one host or the Any host option.
-
Click OK.
How to create a packet filter using custom protocol definitions
-
Open Internet Service Manager.
-
Double-click the computer name alongside the Web Proxy service.
-
The Web Proxy Service Properties dialog box opens.
-
Click the Security button on the Services tab.
-
Click the Packet Filters tab.
-
On the Packet Filters tab, click Add.
-
When the Packet Filter Properties dialog box opens, click the Custom filter option.
-
Select a protocol from the available Protocol ID list.
-
Select a direction from the Direction list.
-
Select an option from the available options in the Local port area.
-
Select either the Any option or Fixed port option in the Remote port area.
-
In the Local host area of the Packet Filter Properties dialog box, select the appropriate option to allow packet exchange with a host.
-
In the Remote host area of the Packet Filter Properties dialog box, specify one host or the Any host option.
-
Click OK.
How to change the packet filter list entries
-
Open Internet Service Manager.
-
Double-click the computer name alongside the Web Proxy service.
-
The Web Proxy Service Properties dialog box opens.
-
Click the Security button on the Service tab.
-
On the Packet Filters tab, click the Enable packet filtering on external interface checkbox.
-
Select the Enable dynamic packet filtering of Microsoft Proxy Server packets checkbox to enable dynamic packet filtering.
-
Click the Edit button.
-
The Packet Filter Properties dialog box opens. Change the necessary settings and then click OK.
-
If you want to remove a filter, click the Remove button.
-
Click OK.
How to configure Proxy Server logging
-
Open Internet Service Manager.
-
Double-click the computer name alongside the Web Proxy service.
-
The Web Proxy Service Properties dialog box opens.
-
Click the Security button on the Service tab.
-
Click the Logging tab.
-
Click the Enable logging using checkbox.
-
Select the appropriate format in the Format list box.
-
Click OK.
How to back up a Proxy Server configuration
-
Open Internet Service Manager.
-
On the View menu item, click Servers View.
-
Double-click the computer name, and then double-click Web Proxy (Running).
-
The Web Proxy Service Properties opens.
-
Click the Service tab.
-
In the Configuration area, click Server Backup.
-
When the Backup dialog box opens, verify the information shown on where the backup file will be saved
-
Click OK to create a back up of the Proxy Server configuration.
How to restore a Proxy Server configuration
-
Open Internet Service Manager.
-
Double-click the computer name, and then double-click Web Proxy service.
-
The Web Proxy Service Properties opens.
-
Click the Service tab.
-
In the Configuration area, click Server Restore.
-
When the Restore Configuration dialog box opens, click the Browse button to select the Proxy Server configuration file.
-
Select the Proxy Server configuration file that you want to use for the restore.
-
Click Open.
-
Select the Full Restore option.
-
When the Restore Configuration dialog box opes, click OK to start the restore of the Proxy Server configuration.

kashyap
i want to know that how to install web proxy?and after how to manage it ?