Understanding the Function of Protocols
Protocols are rules, standards and procedures that enable information to be communicated in the network environment. The rules and standards that control the way in which computers communicate are referred to as protocols.
A few relevant factors to consider when discussing protocols and the network environment are:
- There are numerous protocols
- Each protocol has a specific set of functions that assist in enabling communication over the network.
- The layer of the OSI reference model at which the protocol operates indicates its function.
- Certain protocols can only function at specific layers of the OSI reference model.
- When protocols operate together, they are referred to as a protocol suite or protocol stack.
- Different protocols can operate together at different layers within a protocol stack.
- When protocols support multiple path LAN-to-LAN communications, they are called routable protocols.
- The binding process occurs when protocols are connected to one another and the network interface card (NIC).
- The binding order determines the order in which the operating system runs the protocols.
- A protocol has its own advantages and disadvantages.
The protocol process performed to enable communication, are listed below. The steps are performed at the sending computer from top to bottom. At the receiving computer, this is reversed – the steps are performed from bottom to top.
- The data is broken into smaller chunks of data which the protocol can work with. These chunks of data are called packets. A packet is divided into three segments, which in turn include those components which are listed above:
- Header: The header includes the following:
- A signal which indicates that data is being sent
- Source address
- Destination address
- Clock information needed for synchronization of the data transmission.
- Data: This segment of the packet contains the data which is being sent to the receiving computer.
- Trailer: The trailer segment of a packet normally includes a cyclic redundancy check (CRC) which verifies that the packet is undamaged.
- To identify the destination computer, addressing information is added to the data packets.
- The data is then moved to the network card for transmission over the network.
- At the receiving computer, the data packets are accepted from the network card.
- Any transmission information which was appended to the packet by the sending computer is removed.
- The data is copied from the packets to the buffer so that it can be reassembled.
- The packet is reassembled into the original message and passed to the application.
- Header: The header includes the following:
As mentioned previously, a protocol stack is the grouping of protocols. Within each layer of the protocol stack, specific protocols deal with certain elements and functions that enable computers to communicate.
The protocols in the stack specify the rules at each layer in the OSI model, as follows:
- Application Layer – layer 7; sends a request or receives a request.
- Presentation Layer – layer 6; adds formatting and encryption information to the packet.
- Session Layer – layer 5; adds traffic flow information to the packet
- Transport Layer – layer 4; adds error handling information to the packet.
- Network Layer – layer 3; adds address and sequencing information to the packet.
- Data-Link Layer – layer 2; adds error checking information to the packet. The data is prepared for the connection.
- Physical Layer – layer 1; sends the packet on as a bit stream.
The main standard protocol stacks used in networks today are listed below. At each layer of these protocol stacks, certain protocols work to provide the functions specified for the particular layer.
- TCP/IP
- AppleTalk
- Novell NetWare
- Digital DECnet
- ISO/OSI protocol suite
- Systems Network Architecture (SNA)
Computers communicate using connection-oriented protocols, and connectionless protocols.
- Connectionless protocols: A good example of a connectionless protocol is the User Datagram Protocol (UDP). Connectionless protocols provide no verification that data was delivered. These protocols operate well in networks that have a light load. Connectionless protocols tend to fail in large networks that have a heavy load.
- Connection-orientated protocols: The Transmission Control Protocol (TCP) of the TCP/IP protocol suite is a connection-orientated protocol. Connection-orientated protocols provide verification that data was delivered. These protocols guarantee the reliable delivery of data.
Protocols are categorized as being either of the following three protocol types: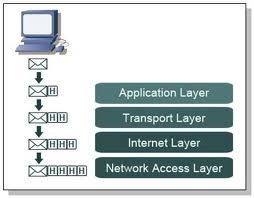
- Application protocols: These protocols enable applications to interact, and data to be exchanged. Application protocols function at the top layer of the OSI model. The well-known application protocols are:
- Advanced Program-to-Program Communication (APPC): This is the peer to peer SNA protocol of IBM that is typically used on AS/400 computers.
- AppleTalk filing Protocol (AFP): This is a remote file access protocol.
- AppleTalk and AppleShare: This is the network protocol suite of AppleTalk.
- Data Access Protocol (DAP): This is a file access protocol.
- File Transfer Access and Management: This is a file access protocol.
- File Transfer Protocol (FTP): This is a Internet file transfer protocol
- Novell NetWare Core Protocol (NCP) and client shells/redirectors: This is a combination of service protocols.
- Server Message Blocks (SMB) and client shells/redirectors: This is a client/server and request/response protocol.
- Simple Mail Transfer Protocol (SMTP): This is an Internet protocol used for sending e-mail.
- Simple Network Management Protocol (SNMP): This is an Internet protocol used to monitor the network.
- Telnet: This is an Internet protocol used to log on to a remote host to enable the local processing of data.
- X.400: This is the CCITT protocol used for sending international e-mail.
- X.500: This is the CCITT protocol used for file and directory services over numerous systems.
- Transport protocols: Transport protocols enable sessions to be established and maintained between computers, and also provide reliable data transport. The main transport protocols are:
- AppleTalk Transaction Protocol (ATP) and Name Binding Protocol (NBP): This is the session and data transport protocols
- NetBIOS extended user interface (NetBEUI): This protocol enables sessions to be established between computers by providing the data transport services.
- NWLink: This is the Microsoft’s implementation of the IPX/SPX protocol.
- SPX: This is the protocol of the Novell IPX/SPX protocol suite for transporting data is a sequential manner.
- TCP: This is the protocol of the TCP/IP protocol that provides the reliable transport of the data.
- Network protocols: These protocols specify the standards for sending information in a certain network environment such as Ethernet. Network protocols provide routing, addressing and error detection functions. The main network protocols are:
- Datagram Delivery Protocol (DDP): This is the data transport protocol of AppleTalk.
- IP: This is the protocol of the TCP/IP protocol that provides packet forwarding and routing.
- IPX: This is the NetWare protocol that provides packet forwarding and routing.
- NetBEUI: This protocol provides data transport for NetBIOS sessions and applications.
- NWLink: This is the Microsoft’s implementation of the IPX/SPX protocol.
An Introduction to the TCP/IP Protocol Suite
TCP/IP is the main protocol suite used to provide interoperability between numerous different types of computers. TCP/IP also supports routing, and is supported by the majority of networks today. The TCP/IP protocol suite was developed by the Advanced Research Projects Agency (ARPA) of the Department of Defense during 1969. The protocol was designed to be routable and efficient.
The main protocols in the TCP/IP suite are:
- Transmission Control Protocol (TCP); the protocol operates at the Transport layer.
- Internet Protocol (IP); the protocol operates at the Network layer.
The other protocols which are specific to the TCP/IP protocol suite are:
- File Transfer Protocol (FTP): This is an Internet file transfer protocol.
- Simple Mail Transfer Protocol (SMTP): This is an Internet protocol used for sending e-mail.
- Simple Network Management Protocol (SNMP): This is an Internet protocol used to monitor the network.
The primary advantages of using TCP/IP are summarized below:
- TCP/IP can be used to establish connections between different types of computers and servers. Providing this type of interoperability is one of the main advantages of TCP/IP.
- TCP/IP is an industry standard, open protocol. This means that it is not controlled by one institute.
- TCP/IP operates independently of the operating system.
- TCP/IP includes support for a number of routing protocols.
- Enables internetworking between organizations.
- TCP/IP has a scalable, client/server architecture.
- TCP/IP includes support for name and address resolution services, including Domain Name Service (DNS) Dynamic Host Configuration Protocol (DHCP) and Windows Internet Name Service (WINS).
Includes support for a number of different Internet standard protocols for Web browsing, file and print services, and for transporting mail.
The disadvantages of TCP/IP are summarized below:
- IPX is faster than TCP/IP.
- TCP/IP is intricate to set up and manage.
- The overhead of TCP/IP is higher than that of IPX.
With TCP/IP, the port numbers to forward messages to the correct application process. Port numbers are assigned by the Internet Assigned Numbers Authority (IANA), and they identify the process to which a particular packet is connected to. Port numbers are found in the packet header.
The TCP/IP protocol suite stems from the DoD model, and therefore matches to the four layers of the DoD model. It does not therefore precisely map to the OSI model. There is however an association between the seven layers of the OSI model and the four layers of TCP/IP model.
The four layers of TCP/IP are listed below and are discussed in the remainder of this Article.
- Network Interface layer
- Internet layer
- Transport layer
- Application layer
The Network Interface Layer
The Network Interface layer of the DoD model is associated with the Physical Layer (layer 1) and the Data-link layer (Layer 2) of the OSI model. The Network Interface layer’s function is to move bits (0s and 1s) over the network medium.
The common methods used to send and receive data are:
- The Carrier Sense Multiple Access/Collision Detection (CSMA/CD) protocol is utilized in Ethernet networks. Devices using CSMA/CD listen for an opening to transmit data. When an opening exists, they send data. By listening for openings on the line, the devices can detect collisions. Collisions occur when a number of devices perceive that an opening exists on the line, and then sends data at the same time. When devices detect a collision, they wait for a random time period before they resend the data. Retransmitting data is normally performed successfully.
- The Carrier Sense Multiple Access/Collision Avoidance (CSMA/CA) protocol is usually utilized in AppleTalk networks. This protocol works much like the CSMA/CD protocol, with the difference being that when an opening is detected to transmit data, the device first sends a signal which indicates to the remainder of the devices that it is going to send data before it starts transmitting the data. The signal serves as a warning to the other devices. While packets containing the warning messages could collide, no collisions occur when the actual data is transmitted. Although the CSMA/CA protocol can detect collisions, the overhead incurred by the protocol is considerable. The recommended method for handling collisions is to use a collision detection method. Collision detection methods are used in Ethernet network technologies.
- Token Passing is usually utilized in Token Ring and FDDI networks. With Token Passing, a signal, called a token passes round the network to each device. A device has to wait for the token before it can send data. In token ring networks, a device only transmits data when it receives the token. While data collisions are prevented, it takes a while for the token to reach each device. Because token ring networks only operate 4Mbps or 16Mbps, the networks are not as popular as the high speed Ethernet networks. FDDI networks use a dual ring topology where traffic moves in opposite directions on the two rings. For networks that need high bandwidth, FDDI is appropriate. FDDI is reliable and faster than Token Ring.
The Internet Layer
The Internet layer of the DoD model handles the packaging, addressing, and routing of data. The Internet layer of the DoD model is associated with the OSI model’s Network layer.
The main protocols of the TCP/IP suite that operate at the Internet layer are:
- Internet Protocol (IP): IP is a connectionless, routable protocol which performs addressing and routing functions. IP also places data into packets, and removes data from packets. When data is sent using a connectionless process, it is called datagrams. IP packets include the following data:
- Source IP address; this address identifies the computer sending the datagram.
- Destination IP address; this address identifies the receiver of the datagram.
- Identification; which define a particular IP datagram. If the datagram was fragmented, it defines all fragments of the particular IP datagram.
- Protocol; specifies the protocols that the receiving IP should pass the IP packet.
- Checksum; a method used to verify the integrity of the IP header.
- Time-to-Live (TTL); indicates how many networks the datagram can move through before it is dropped.
- Internet Control Message Protocol (ICMP): The protocol is responsible for dealing with errors associated with undeliverable IP packets, and for indicating network congestion and timeout conditions. The sending computer receives a Destination Unreachable message, such as the Network Unreachable message or Port Unreachable message from ICMP when a message is not delivered. Source Quench messages are returned to the sending device by ICMP to indicate network congestion.
- Internet Group Management Protocol (IGMP): The IGMP protocol controls host membership in groups of devices, called IP multicast groups. The devices in the IP multicast groups receive traffic which is addressed to a shared multicast IP address. The traffic is then processed by multiple IP hosts. Multicasting is the process which enables a server to send the identical data to multiple computers simultaneously. Unicast messages are sent to a host, while a multicast is sent to each member of an IP multicast group. IGMP permits the different message types used to create multicast groups and to transmit multicast messages.
- Address Resolution Protocol (ARP): The ARP protocol maintains the associations which map IP addresses to MAC addresses. Because mappings are stored in the ARP Cache, when the same IP address needs to be mapped again to its associated MAC address, the discovery process is not performed again. The messages which the ARP protocol uses are:
- ARP request message
- ARP reply message
- RARP request message
- RARP reply message
Reverse Address Resolution (RARP) resolves MAC addresses to IP addresses.
The Host to Host Layer
The Host to Host layer of the DoD model manages the transportation of data, and establishes the connection between hosts to exchange already formatted data. This layer is associated with the Transport layer of the OSI model.
The main TCP/IP protocols operating at the Host to Host or Transport layer are:
- Transmission Control Protocol (TCP): TCP offers greater reliability when it comes to transporting data than what UDP, the other TCP/IP protocol which works at this level provides. With TCP, the application which sends the data receives acknowledgement or verification that the data was actually received. TCP is regarded as a connection-orientated protocol – a connection is established before data is transmitted. TCP performs the following key functions when transmitting packets over the network:
- Segments the packets: Data is sent in segments over the network. Each segment has a sequence number.
- Acknowledges transmitted packets: An acknowledgement message is sent by the receiving host to the sender when the data is received.
- Assist in the recovery of lost packets: When an acknowledgement message is not returned by the receiving computer in a certain time frame, the data is assumed lost and is then resent.
- The TCP port to transmit the data.
- The TCP port to receive the data.
- The sequence number for the segment.
- The acknowledgement number
- The window size
- The client computer sends a synchronization request message, and the sequence number which it generates.
- The server computer responds by sending an acknowledgement message. The original sequence number is included with 1 added to it. The server sends its SYN number as well.
- The client adds 1 to the SYN number of the server. This is returned to the server as an ACK (acknowledgement).
A TCP segment has a header, which includes the following information:
With TCP, a three-part TCP handshake process is performed to establish a host to host connection. The three-part TCP handshake process establishes a reliable connection over which to exchange data:
- User Datagram Protocol (UDP): UDP does not provide reliable data transport. No acknowledgements are transmitted. While UDP is faster than TCP, it is less reliable. The fields included in the UDP header are:
- Source port
- Destination port
- UDP Checksum
TCP and UDP utilize port numbers to forward messages to the correct application process. Port numbers are assigned by the Internet Assigned Numbers Authority (IANA). They identify the process to which a particular packet is connected to, and are found in the packet headers. Numerous well-known TCP and UDP ports exist.
The main port numbers are:
- Port 20; for File Transfer Protocol (FTP) data
- Port 21; for File Transfer Protocol (FTP) control
- Port 23; for Telnet.
- Port 25; for Simple Mail Transfer Protocol (SMTP)
- Port 80; for Hypertext Transfer Protocol (HTTP)
- Port 88; for Kerberos
- Port 110; for Post Office Protocol (POP3) – version 3
- Port 443; for Secure HTTP (HTTPS)
The Application Layer
The Application layer of the DoD model is associated with the Session layer, Presentation layer, and Application layer of the OSI model. Therefore, application layer protocols of the TCP/IP protocol suite functions at these layers. Application layer protocols enable applications to communicate between each other, and also provide access to the services of the lower layers.
The main application layer protocols and services which function at the Application layer of the OSI model are explained below:
- NetBIOS over TCP: This is a group of application layer protocols that provide the following services for NetBIOS applications
- Name service: This service enables host computers to attain and retain a particular host name. The name service utilizes UDP Port 137. The name service is responsible for resolving a NetBIOS name to an IP address.
- Session service: This service enables messages to be exchanged, reliably, between two NetBIOS applications. The service utilizes TCP Port 139.
- Datagram service: This service provides connectionless and unreliable message sending between two NetBIOS applications. The datagram service utilizes UDP port 138.
- Windows Sockets: This is the Windows Application Programming Interface (API) which provides the standard programming interface to access standard TCP/IP functionality in Windows. The Windows tools that are use Windows Sockets are:
- DHCP servers and clients
- FTP servers and clients
- Telnet client
- Packet InterNet Groper – ping
- Trace Route – tracert
- Server Message Block/Common Internet File System: The SMB (Server Message Block) protocol was developed in the 1980s by IBM. SMB was initially designed to be used for file and print sharing. The Common Internet File System (CIFS) protocol stemmed from the SMB protocol. CIFS is an operating system independent protocol that can be used by many different platforms and operating systems. It also functions across network and transport protocols.
- Internet Printing Protocol (IPP): The IPP protocol is connected to the Server Message Block (SMB) and Common Internet File System (CIFS) protocols, and enables printing operations to be performed across the network via HTTP version 1.1. For IPP to work in Windows Server 2003, the IPP Server has to be running Internet Information Services 6 (IIS 6.0).
- Telnet: This is a terminal emulation protocol that makes it possible for you to log onto a remote computer that is using TCP/IP, and running the Telnet Server service. In Windows Server 2003, the Telnet Server service is not by default started. In order to log on to a remote host, the Telnet client must have a username and password for the remote computer.
- Windows Internet Name Service (WINS): WINS cannot be used on non-Microsoft operating system based computers. WINS is a NetBIOS name server used by NetBIOS clients to resolve, register and obtain NetBIOS names. WINS is implemented via the following two services:
- Server service: The Server service performs the following functions:
- Manages the database that stores the NetBIOS names and IP addresses mappings
- Replicates the database to the other WINS Servers.
- Client service: The Client service performs the following functions:
- Registers the computer name via WINS
- Provides name resolution services to local applications and services.
Each of the Windows Server 2003 Editions includes the WINS service. By default, the service is though not installed.
- Server service: The Server service performs the following functions:
- Dynamic Host Configuration Protocol (DHCP): The DHCP protocol assigns IP addresses to computers on TCP/IP networks. By dynamically assigning IP addresses to host computes, DHCP eliminates the need for manually assigning IP addresses and it also prevents the duplication of IP address assignments. DHCP also ensures that all assigned IP addresses are unique. DHCP manages a database of the IP addresses it assigns to host computers. DHCP has the following components:
- Server service: The Server service performs the following functions:
- Assigns IP address to host computers.
- Manages the database which contains IP address assignment information.
- Client service: The Client service communicates with the Server service when an IP address is requested. It also configures information such as subnet mask and default gateway.
- Server service: The Server service performs the following functions:
- Domain Naming System (DNS): DNS resolves host names to an IP addresses so that packet delivery can take place. In fact, in Windows Server 2003, DNS is the main method used to resolve host names to IP addresses. For backward compatibility, Windows Server 2003 includes support for hosts file.
- Routing Information Protocol (RIP): RIP is a routing protocol that is used to exchange routing information among RIP routers. RIP works well in small to medium sized networks.
- Simple Mail Transport Protocol (SMTP): The SMTP protocol operates at the Application layer, and is used to transmit e-mail messages and attachments between e-mail servers and from e-mail clients to e-mail servers.
- Network News Transfer Protocol (NNTP): NNTP enables servers and clients to exchange information in the form of news articles. Through the NNTP service, you can implement private news servers to host discussion groups, or you can implement public news servers to provide customer support and help resources to Internet users. You can specify that users need to be authenticated to both read and post items to newsgroups, or you can allow access to everybody. The NNTP service can also integrate with the Windows Indexing Service for indexing of newsgroup content. NNTP is implemented as a client/server protocol.
- The news server manages the news clients and articles.
- The NNTP server service is an IIS component that can host news groups.
- Post Office Protocol (POP): POP is an e-mail application protocol that is used to retrieve e-mail from e-mail servers for the client applications.
- Internet Message Access Protocol (IMAP): IMAP is also used to retrieve e-mail from e-mail servers. The difference between POP and IMAP is that IMAP allows client programs to access the e-mail on the server, and users can read, delete, and reply to messages on the server. IMAP therefore does not require users to download mail to their client computers.
- File Transfer Protocol (FTP): FTP is used to transfer files between hosts. FTP is typically used to transfer files on the Internet.
Hypertext Transport Protocol (HTTP): This is the protocol, defined in 1990 which is used to transfer files used on the Internet to access Web pages. HTTP is implemented as a HTTP Server and a HTTP Client. The HTTP Server functionality is provided by IIS. The HTTP Client functionality is provided by Web browsers such as Microsoft Internet Explorer and Netscape Navigator. - Simple Network Management Protocol (SNMP): This is a regarded as a network management protocol because it is used to enable communication between a network management console and a device on the network. SNMP enables control information to be shared with the network management console. To enable network management information to be shared, SNMP utilizes a system/agent framework.
Linux TCP/IP Network Administration
Linux is a secure, scalable, dependable and reliable operating system based on shell programming. Linux also has a default support of TCP/IP protocol suite. The network administration of Linux is based on TCP/IP. You can use the TCP/IP tool “netconfig” for configuring the network interface card in Linux.
Alternatives to TCP/IP
Although the TCP/IP is the most popular protocol suite used in the network or internetwork communication but there are some other protocol suite also can be used as an alternative of TCP/IP. One of the alternatives is the Novell IPX/SPX protocol suite in which the IPX (Internet Packet Exchange) works at 3rd layer of OSI layer Model like IP in TCP/IP and SPX (Sequenced Packet Exchange) works at 4rth layer of OSI Model like TCP in the TCP/IP protocol suite. AppleTalk and DECNET are the other popular alternatives of the TCP/IP.



Henry
Dear Tech Faq,
You have written a VERY comprehensive article. I has more information than I came looking for but it is better to have more than less. I liked your explanation of all the different protocols. Thank you for providing the information.
Henry
Timmy
How do I cite this article?